Elliott Kember, has a post on his blog right now discussing an apparent “security vulnerability” in Chrome. Â Security Vulnerability is in quotes there, not to mock Mr. Kember, but because the behavior Chrome exhibits is debateable as either vulnerability or feature. Â First, let’s walk through the behavior.
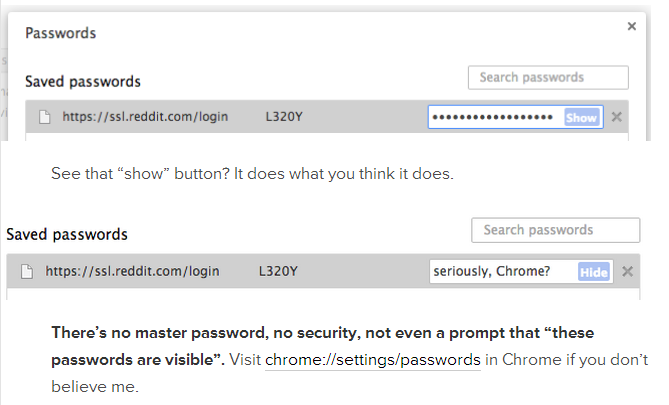
If you’ve saved passwords into Chrome, navigate to chrome://settings/passwords and click on a row.  You’ll see a “show” button which, when clicked, displays your saved password.I’m lazy, so I’ll just screenshot Kember’s blog:
Now Kember thinks this is a serious problem and he might be right. Â Most users probably don’t think that when they save their password to their browser that someone can trivially just open a window and copy their passwords. Â Kember holds that Chrome should require some kind of master password or key to prevent exposing these passwords to prying eyes and certainly that would at least keep users from casually browsing a person’s stored password file.
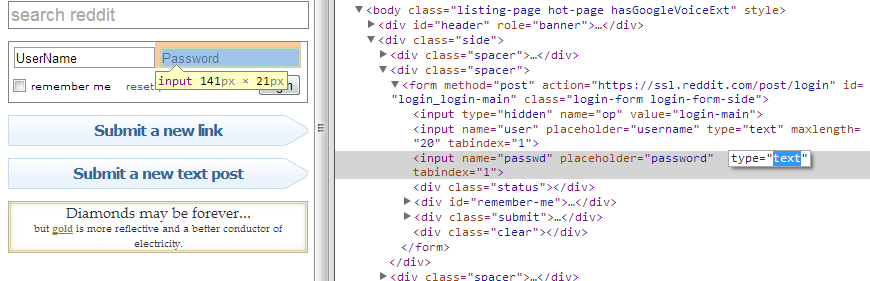
But there’s a flip side too. Â Even if Chrome didn’t have this screen there would still be a fairly easy way to compel the browser to cough up its passwords. Â Chrome’s built-in designer tools can allow you to change a password box to a text box, thereby exposing the password.
This is a vulnerability that exists in every browser that saves passwords.  The nature of the field means that the browser must supply the password as if it were typed by a human.  Chrome’s designers made a decision not to deceive their users into believing that their stored passwords were more secure than they really are.
Who’s right? Â Who’s wrong?
Well, neither really. Â The correct answer to this problem is to prevent the filling of these boxes and thus the opening of that security hole without the user’s permission. Â Simply put, Chrome and other browsers should do what third-party password management tools like 1Pass and LastPass do: prompt the user for a master password before filling in any details.
Getting users to exercise good password discipline is hard enough without companies like Google undercutting good practices. Â Chrome is a heck of a browser and it is hardly alone in exposing this vulnerability, but the industry standard is no excuse.